Why Silent Circle?
Most encrypted messaging apps are built for consumers. Silent Circle is built for people whose communications cannot afford to leak — executives, journalists, lawyers, government officials, and security professionals.
The difference is not just encryption strength. It is architecture. Silent Circle operates its own secure infrastructure, conducts regular third-party audits, and is headquartered in Switzerland — outside the jurisdiction of mass surveillance programs.
Silent Circle is trusted by:
• Fortune 500 companies for executive communications
• Government agencies in over 100 countries
• NGOs operating in hostile environments
• Journalists protecting sources in high-risk regions
• Active since 2003 with a strong cryptography team
Key features
Unlimited Peer-to-Peer Calling
Unlimited talk, text, video and conference calls between Silent Phone members. No limits, no per-minute charges, no compromises.
End-to-End Encrypted and Authenticated
Silent Phone ensures your chats are completely private and only between you and the other person. All encryption happens on your device. Nobody can eavesdrop — not even Silent Circle.
Data Minimization
Storing too much data can be risky. While many providers save extra data "just in case," Silent Circle only keeps what is absolutely necessary. No IP address tracking, no call logs, no message logs between users.
What is included
Encrypted voice calls — Crystal-clear calls with end-to-end encryption. No recordings, no logs, no metadata.
Encrypted video calls — Face-to-face meetings without the risk. Works globally.
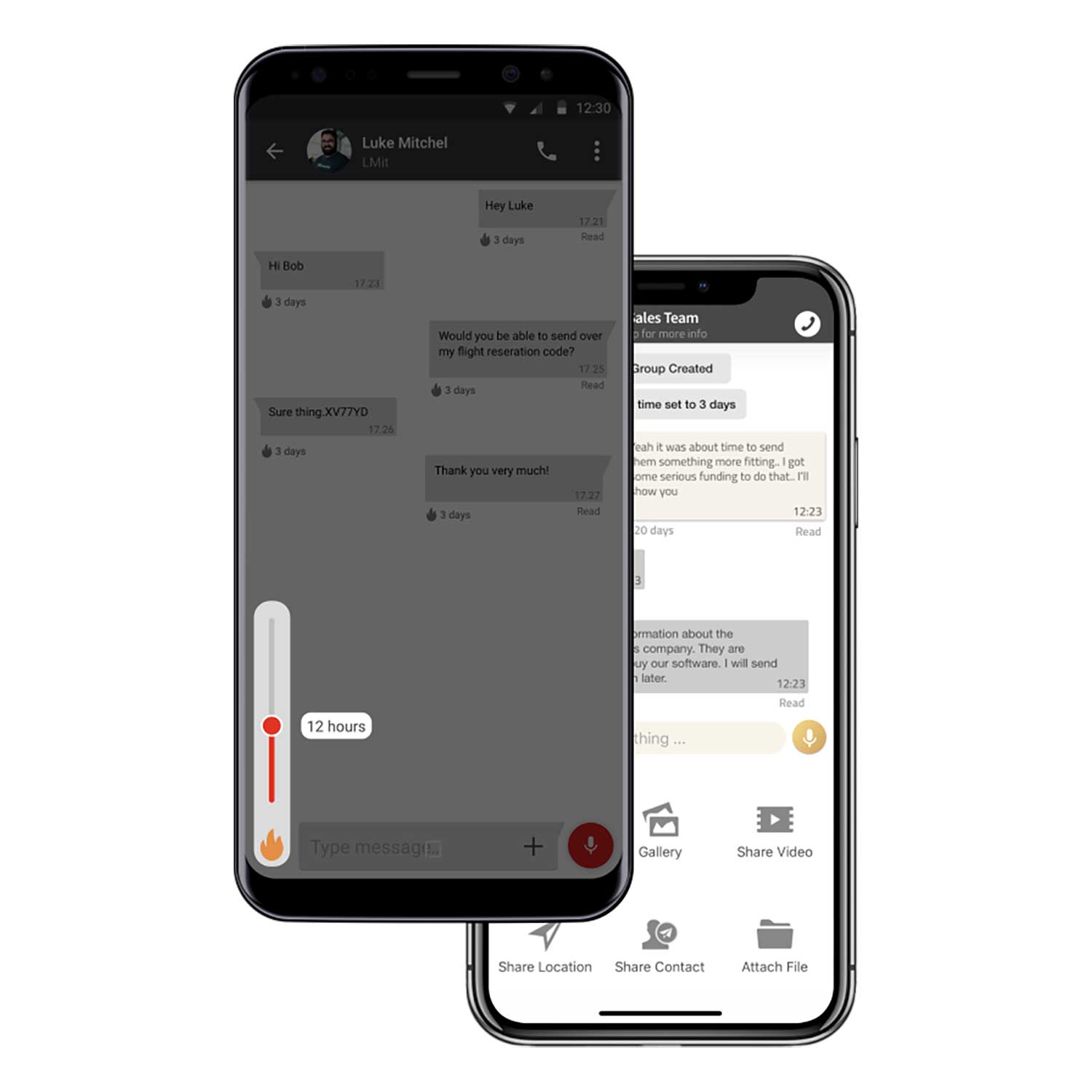
Secure messaging — Text, voice messages, and file sharing up to 100MB with full Burn functionality.
Conference calls — Multi-party encrypted calls for team coordination.
File transfer — Send documents and files with the same encryption as your calls.
Silent Circle vs Signal
Signal is excellent — and free. So why pay for Silent Circle?
• Enterprise management — Admin controls, user provisioning, compliance features
• Dedicated infrastructure — Silent Circle runs its own servers
• Swiss jurisdiction — Stronger legal protection than US-based services
• Support — Actual support team, not community forums
• Conference calls — Native encrypted group calls
For personal use, Signal is often enough. For professional use where communications could be subpoenaed or intercepted — Silent Circle is the standard.
How it works
1. Choose your plan — Select 3, 6, or 12 months.
2. We deliver your license — Voucher code sent via your preferred messenger (Email, WhatsApp, Signal, or Telegram).
3. Install and activate — Download Silent Phone, enter your code. Works on Android, iOS, Silent OS, and CryptPhones.
4. Communicate securely — Call and message with full encryption.
Works perfectly with CryptPhones
Silent Circle is pre-vetted for our GrapheneOS devices. Running Silent Phone on a CryptPhone gives you two layers of protection: an operating system that does not spy on you, and communications that cannot be intercepted.
We can pre-install and configure Silent Circle on your CryptPhone before shipping — just ask.
Frequently asked questions
How do I receive my license?
After purchase, we send your Silent Circle voucher code via your chosen messenger — Email, WhatsApp, Signal, or Telegram. The code can be used for activation or to top up your existing account. No account linking with Cryptvice, no paper trail.
Can I call people who do not have Silent Circle?
Yes. Silent Circle supports outbound calls to regular phone numbers through secure SRTP. However, only calls between Silent Circle users are fully end-to-end encrypted.
Does Silent Circle work on iPhone?
Yes. Silent Phone is available for iOS, Android, and Silent OS. For maximum privacy, we recommend using it on a CryptPhone where the OS itself does not track you.
What happens when my license expires?
Your app continues working for receiving calls and messages, but you cannot initiate new communications until you renew. Message history remains encrypted on your device.
Is Silent Circle anonymous?
Silent Circle does not require personal information to activate. Combined with purchasing through Cryptvice (crypto accepted), you can use it with minimal identity exposure.
What is Burn functionality?
Burn allows you to set messages and files to automatically delete after a specified time — from seconds to days. Once burned, the content is permanently deleted from both devices.